experts and translators of the new domain
Media
 From Worms to Cyber War
From Worms to Cyber War
By Paul Rosenzweig
In just a generation, viruses went from being a novelty to a worldwide threat.
Editor’s note: This article is the second in a series of three articles about cybersecurity and cyberwarfare that will be published periodically in Defining Ideas. The first article, Cybersecurity: An Introduction, can be found at the following link.
The first known virus ever to infect a personal computer was named “Brain.A.” It was developed (dare we say invented?) by two Pakistani brothers Basit and Amjad Alvi. We know this because, amusingly, they signed their work and included contact information in the code of the virus. Brain. A was first detected in January 1986, just over 25 years ago. In its initial form, the virus did no significant harm. It renamed a volume label (in effect a file name) to “Brain” and could freeze a computer. Basit and Amjad say they meant no harm from their creation. How the world has changed! In just a single generation, we have gone from viruses being a novelty, to them being very real threats to cyberspace.
The first notable damaging “attack” on the web occurred by accident, though it was a purposeful accident, if that makes any sense. In late 1988, a Cornell graduate student, Robert Tappan Morris, released a worm intended to demonstrate flaws in the security protocols of the early internet. A worm, as its name implies, burrows through legitimate programs and hides in the dirt of computer code, so to speak. This worm was designed to enter through a security gap, replicate itself, and then move onward to infect more computers. Because of a design flaw in the worm, it spread like wildfire and caused significant damage, effectively clogging the entire internet and preventing information from being transmitted (the internet was much smaller back then). In fact, when Morris realized that he had made a mistake, he tried to send out messages to other internet users telling them how to kill the worm—but his own messages of warning were blocked by the congestion his worm had caused.
Today, the Morris worm would be a mere pinprick. The cyber domain has not yet reached the state where interconnectedness is so great that a Die Hard IV scenario is plausible (for those who have not seen the movie, it imagines a mad cyber scientist who takes down all of the electric and transportation networks of the United States, only to be beat up by Bruce Willis). But the vulnerabilities to both intrusion and attack are real. Criminal theft and espionage occur at the billion dollar-per-terabyte level. And “cyber hacktivists” have waged proxy wars on behalf of Russia against Estonia and Georgia. All educated internet users need to understand what the nature of the threat is and the distinction between intrusions and attacks.
The first notable cyberattack occurred by accident.
 In real economic terms, cyber crime is the dominant threat in cyberspace. Everyone by now is familiar with the prevalence of simple Nigerian scams—nobody should fall for them anymore, or so one would hope. But that, unfortunately, is not the case – they are still quite successful. The costs to the scammer of making the effort are so miniscule (pennies for millions of spam sent) that even a tiny success rate makes the scam worthwhile. When the cost-benefit ratio is so skewed by technology in favor of the fraudsters, it is no wonder that fraud continues.
In real economic terms, cyber crime is the dominant threat in cyberspace. Everyone by now is familiar with the prevalence of simple Nigerian scams—nobody should fall for them anymore, or so one would hope. But that, unfortunately, is not the case – they are still quite successful. The costs to the scammer of making the effort are so miniscule (pennies for millions of spam sent) that even a tiny success rate makes the scam worthwhile. When the cost-benefit ratio is so skewed by technology in favor of the fraudsters, it is no wonder that fraud continues.
It is hard to get firm estimates of losses from cyber crime, but the figures are significant: According to the Government Accountability Office, in 2006 the FBI estimated that the annual loss due to computer crime was approximately $67.2 billion for U.S. organizations. The estimated losses associated with particular crimes include $49.3 billion for identity theft and $1 billion annually due to phishing (that is, tricking someone into giving you a password). The pattern is repeated around the world—Detica estimates total cyber-related losses in the United Kingdom last year at £27 billion. One caveat is important: Most of these losses are from the theft of intellectual property (a real loss to be sure). Direct monetary losses are roughly an order of magnitude less—“only” £3.7 billion annually in the UK, for example.
The absolute volume of the malfeasant activity on the internet sometimes defies human understanding. One study from 2010 of internet traffic on the Bell Canada network found over 53 gigabytes per second (!) contained malicious code of some sort (this is roughly 17 percent of the total traffic load on the Canadian internet at any moment). Likewise, the security firm Symantec discovered 286 million new unique malicious threats in 2010, or roughly nine new malware creations every second. As Noah Shachtman recently put it, even putting aside the more existential threats from cyber war or cyber espionage, the growth of crime on the internet is quickly making the network a bit like the South Bronx in the late 1970s—a place that no reasonably sensible person would want to go.
Botnets can be weapons of war. They can crack codes and attack infrastructure systems.
One of the most virulent forms of malevolent activity on the net these days is the “botnet,” a network of infected “zombie” computers, whose operations can be controlled by someone other than the true owner. When a botnet worm infects a computer, it plants controlling software that allows the botnet controller to give orders to the computer. Then it moves on, looking for other computers to infect. And all of the infected computers with a particular botnet infection can, when linked together, be given a collective order. There are thousands of botnets in the world—and they are so easy to create and maintain that members of the Russian Business Network (a criminal computer cartel) rent out botnets for a fee. But most botnets are small—only a few thousand computers are linked at a time. The largest known botnet, named “Conficker,” links upwards of 10 million computers—and though we’ve identified it, nobody knows how to defuse it or what its ultimate purpose is.
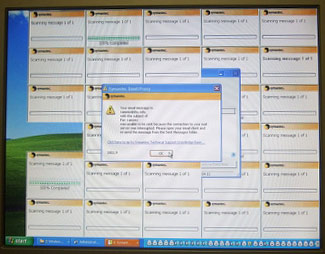
Why are botnets a risk? They can be used to pass around more malware; or steal information. They can be used for a denial of service attack—where a server is overwhelmed by spam messages so that legitimate messages can’t get through. That’s the tactic that the hacktivist group “Anonymous” used to target Amazon and PayPal last year. Once created, botnets are valuable tools for criminal enterprise. But botnets can also be weapons of war—working together, they can crack codes and passwords and attack critical infrastructure systems, like the banking system or the electric grid. What’s particularly scary about Conficker, for example, is that nobody knows who owns it or operates it or what they plan to do with it.
And, of course, crime is not the only malevolent act in cyberspace. The threats to industrial security and national security are real, but even more difficult to measure. To cite one incident, consider the recently analyzed GhostNet malware. That malware imported a Trojan horse program onto infected computers which allowed a remote user to, effectively, control the computer. The remote user could activate a keystroke logger, turn on the computer’s video camera or microphone, and, of course, exfiltrate any data stored on the computer. First observed on computers operated by the Dalai Lama, the malware was found in dozens of other computers including some located in the embassies of India, Malaysia, and Indonesia, ministries of foreign affairs, and even NATO (SHAPE) headquarters (albeit on an unclassified system). Extended analysis eventually traced the malware to an internet address on a Hainan Island off the coast of China, an island that, perhaps coincidentally, is home to the headquarters of China’s signals intelligence agency.
With the growth of cyber crime, the internet resembles the South Bronx of the late 1970s.
Or, consider the cyber war waged by Russian hacktivists against first Estonia and then Georgia. In August 2008, for example, when Russian troops conducted a land war against Georgia, Russian “cyber patriots” waged a cyber campaign against Georgia. The campaign was powered by the botnet world and involved mostly denial of service attacks against Georgian websites (like the website for Georgia’s Ministry of Foreign Affairs), as well as website defacement. According to the US Cyber-Consequences Unit (a study group set up to assess cyber events), the attacks were the work of civilians who, though not directed by the Russian military, had advance knowledge of the land attack so that they were able to pre-plan and organize the cyber-effort. The civilian hacktivists used social media to organize their efforts.
It is difficult to assess how significant these incidents have been. But whatever their costs, theorists used to take comfort in the fact that cyber attacks only had cyber effects. As one wag put it, “the only thing that dies in a cyber attack is a bunch of baby electrons.” In the absence of physical damage, cyber consequences were thought to be highly confounding, but manageable.
No longer. Last year, observers around the world took notice when a piece of malware known as Stuxnet was discovered that had significant effects on the capabilities of the Iranian nuclear program. The program operated by affecting the rate at which nuclear centrifuges spun. In order to produce uranium suitable for use in a nuclear bomb (or, for that matter, in a nuclear power plant), the centrifuges must run at a constant rate. Stuxnet caused the centrifuges to run at a highly variable rate, while falsely reporting to the operators that everything was in working order.
Nobody knows who built Stuxnet, but it is the first release “in the wild” of a program that can physically effect the operation of a major industrial plant. Many speculate that it was developed by the Israelis with American assistance, but there is no direct proof of that. Whatever its source, Stuxnet’s significance is that it shows incorporeal software can have real world, kinetic effects. The only difference between a worm that changes how centrifuges run and one that forces, say, a generator, to run itself to death and blow up, or causes a chemical plant to release a hazardous chemical, is the alteration of a few lines of code.
Stuxnet was proof that cyber war can be real. As the Department of Homeland Security recently noted: “attackers could use the increasingly public information about the [Stuxnet] code to develop variants targeted at broader installations of programmable equipment in control systems.” In short, we now face the prospect of cyber attacks that destroy real things (like the electric grid). That ought to give everyone pause.
Paul Rosenzweig, Esq., is the founder of Red Branch Law & Consulting, PLLC. Rosenzweig formerly served as deputy assistant secretary for policy in the Department of Homeland Security and twice as acting assistant secretary for international affairs. Rosenzweig is a professorial lecturer in Law at George Washington University and a visiting fellow at the Heritage Foundation. He serves as a senior editor of the Journal of National Security Law & Policy.
Rosenzweig is a cum laude graduate of the University of Chicago Law School. He is the coauthor (with James Jay Carafano) of the book Winning the Long War: Lessons from the Cold War for Defeating Terrorism and Preserving Freedom and author of the book Cyberwarfare: How Conflicts in Cyberspace Are Challenging America and Changing the World.
The essay above is based on a book by the author titled, Cyberwarfare: How Conflicts in Cyberspace are Challenging America and Changing the World.
Letters to the editor may be sent to definingideas@stanford.edu. Editors reserve the right to reject or publish (and edit) letters.
